In part one of our series, we established how the Identity Access Management (IAM) environment is bolstered by the addition of a multi-factor authentication (MFA) process. Up next is how to choose the best MFA option for your specific environment.
Multi-Factor Authentication methods are generally divided into five categories each of which have their own unique benefits and challenges.
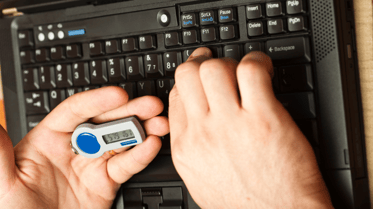
This method of authentication uses hardware-based devices to generate one-time codes based on a cryptographic key. In many cases, the password is delivered via a fob-like device with a built-in screen or a key padded device that requires the user to add a PIN to access the OTP. The key is simultaneously held by a server which in turn generates the same OTP to verify that the code provided by the user is correct. While generally effective, this form of authentication can present some challenges from a lack of scalability to the high cost of deployment and maintenance. Perhaps the most notable issue however is this method’s vulnerability to misplacement, theft, and even social engineering or impersonation attacks.
-
Standalone OTP Mobile Applications
Authenticator apps generate time-based, OTP that refreshes every 30 seconds. The user is then required to enter or paste this into the secured app or site before being granted access. Barring minor user experience issues which require users to switch between apps to authenticate, these mobile authenticator apps succeed where hardware tokens fall short providing greater simplicity, accessibility, convenience, and flexibility in addition to the obvious security benefits.
.png?width=395&name=Untitled%20design%20(1).png) While authenticator apps have become a very popular authentication method choosing the right one will depend on the specific needs of your organization’s IAM environment. Does your app offer an encrypted backup? An app like Authy or Last Pass offers such services which could be helpful if you are no longer in possession of the device that the account was initially set up on. Does your mobile authenticator prevent you from taking screenshots as an added layer of security? If you’re securing data for a financial institution, then an android device running Google’s Mobile OS could be particularly useful.
While authenticator apps have become a very popular authentication method choosing the right one will depend on the specific needs of your organization’s IAM environment. Does your app offer an encrypted backup? An app like Authy or Last Pass offers such services which could be helpful if you are no longer in possession of the device that the account was initially set up on. Does your mobile authenticator prevent you from taking screenshots as an added layer of security? If you’re securing data for a financial institution, then an android device running Google’s Mobile OS could be particularly useful.
-
Soft Token Software Development Kits (SDKs)

This is software that can be embedded into mobile apps and utilizes cryptographic operations such as digital signatures to authenticate the user and device. Soft tokens have the added convenience of a smoother user experience (UX). by removing the need to switch between apps or rely on a hardware device.
-
SMS-Based OTPs
This form of authentication is a user-friendly option because it does not require the end-user to install any apps. Instead, users are sent a one-time password sent by SMS text message to their phone. That password is then used to authenticate them. This option is not without its limitations most of which are the result of challenges with the mobile carrier. This option can also be vulnerable to malware attacks or even SIM-swapping.
-
Smartcards & Cryptographic Hardware Tokens
This authentication method can cause some real operational challenges for businesses including a high cost of deployment, maintenance, upgrades, and replacement. Like OTP Hardware tokens, physical devices can be lost or misplaced however from a security standpoint this method offers devices that can perform cryptographic operations like decryption and signing while providing strong physical protection of the keys inside a fully isolated secure enclave. They can be used for logon to PCs in addition to being used to digitally sign transactions. Smartcards may require a dedicated reader but can also be contactless with cryptographic hardware tokens which are typically connected via USB.
So what have we learned? Well, what is clear is that no matter which type of MFA authentication method you choose, there are both pros and cons. Each MFA method has its set of challenges but all attempt to strike the balance between security and usability.
In the third and final part of our series on Multi-factor Authentication, our experts clue us in on their preferred MFA platform, how we use it and how it can help secure your organization.